Network-Security
Question 1 |
A sender is employing public key cryptography to send a secret message to a receiver. Which one of the following statements is TRUE?
Sender encrypts using receiver’s public key | |
Sender encrypts using his own public key | |
Receiver decrypts using sender’s public key | |
Receiver decrypts using his own public key |
Question 2 |
Which of the following statement(s) is TRUE?
1. A hash function takes a message of arbitrary length and generates a fixed length code.
2. A hash function takes a message of fixed length and generates a code of variable length.
3. A hash function may give the same hash value for distinct messages.
1 only | |
2 and 3 only | |
1 and 3 only | |
2 only |
(2) Statement-2 is wrong, refer statement-1.
(3) Statement-3 is correct, for example hash function N%10, this will generate same values for 1 as well as 2!
Question 3 |
Consider the following two statements:
(i) A hash function (these are often used for computing digital signatures) is an injective function.
(ii) An encryption technique such as DES performs a permutation on the elements of its input alphabet.
Which one of the following options is valid for the above two statements?
Both are false | |
Statement (i) is true and the other is false | |
Statement (ii) is true and the other is false | |
Both are true |
ii) It uses the P-Box permutation.
Statement-I is false, II is true.
Question 4 |
Your are given the following four bytes :
10100011 00110111 11101001 10101011Which of the following are substrings of the base 64 encoding of the above four bytes?
zdp | |
fpq | |
qwA | |
oze |
10100011 00110111 11101001 10101011
So, in total we have 32 bits. And for base 64 we need 6 digits of binary no. to represent one digit of base 64 no.
So lets padd 4 bits on RHS, so that total digits will become 36 and we can separate then as group of 6 digits each.

Now, the longest substring will be from checking option is 'fpq'.
Question 5 |
The total number of keys required for a set of n individuals to be able to communicate with each other using secret key and public key crypto-systems, respectively are:
n(n-1) and 2n | |
2n and n(n-1)/2 | |
n(n-1)/2 and 2n | |
n(n-1)/2 and n |
nC2 = n(n-1)/2
In case of public key, each sender has its own public key as well as private key. So, no. of keys are 2n.
Question 6 |
2N | |
N(N – 1) | |
N(N – 1)/2 | |
(N – 1)2 |
(N 2) = N(N – 1)/2
The number of keys required in the system as a whole to satisfy the confidentiality requirement is:
N(N – 1)/2
Question 7 |
The value of 351 mod 5 is ______.
3 | |
5 | |
2 | |
1 |
⇒ 31 = 3 ⇒ 3 mod 5 = 3
32 ⇒ 9 mod 5 = 4
33 ⇒ 27 mod 5 = 2
34 ⇒ 81 mod 5 = 1
35 ⇒ 243 mod 5 = 3
For every four numbers sequence is repeating.
So, (51 % 4) = 3
⇒ 33 = 27
⇒ 27 mod 5 = 2
Question 8 |
In an RSA cryptosystem, the value of the public modulus parameter n is 3007. If it is also known that Φ(n) = 2880, where Φ() denotes Euler's Quotient Function, then the prime factor of n which is greater than 50 is ______.
107 | |
97 | |
45 | |
92 |
n = 3007, fi(n) = 2880 → fi(n) = (p – 1) (q – 1),
where p, q are prime factor of n.
The unit place of n is 7, it is a prime number and factor will be
1.7=7
11*17
21*37
31*47
….
31*97 =>3007
n = 3007 => 31*97
Therefore, 31 & 97 are the two prime numbers, which is satisfying the condition and 97 is greater than 50.
So, 97 is the correct answer.
Other methods:
When ϕ(n) is given when n=pq where p and q are prime numbers, then we have
ϕ(n) = (p−1)(q−1) = pq−(p+q)+1
But pq=n,
therefore, ϕ(n) = n−(p+q)+1 and p+q = n+1−ϕ(n).
Now, p and q are the roots of the equation,
x2 − (p+q)x + pq = (x-p)(x-q)
Substituting for p+q and pq in the above equation
x2 - (n+1-ϕ(n))x + n
Question 9 |
In the RSA public key cryptosystem, the private and public keys are (e, n) and (d, n) respectively, where n = p*q and p and q are large primes. Besides, n is public and p and q are private. Let M be an integer such that 0 < M < n and f(n) = (p- 1)(q-1). Now consider the following equations.
I. M’= Me mod n
M = (M’)d mod n
II. ed ≡ 1 mod n
III. ed ≡ 1 mod f(n)
IV. M’= Me mod f(n)
M = (M’)d mod f(n)
Which of the above equations correctly represent RSA cryptosystem?
I and II | |
I and III | |
II and IV | |
III and IV |
1. Generate randomly two “large” primes p and q.
2. Compute n=pq and ∅=(p-1)(q-1).
3. Choose a number e so that
gcd(e,∅)=1
4. Find the multiplicative inverse of e modulo ∅, i.e., find d so that
ed≡1 (mod ∅)
This can be done efficiently using Euclid’s Extended Algorithm.
The encryption public key is KE=(n,e) and the decryption private key is KD=(n,d).
The encryption function is
E(M)=Me mod n
The decryption function is
D(M)=Md mod n
Question 10 |
A layer-4 firewall (a device that can look at all protocol headers up to the transport layer) CANNOT
block entire HTTP traffic during 9:00PM and 5:00AM | |
block all ICMP traffic | |
stop incoming traffic from a specific IP address but allow outgoing traffic to the same IP address | |
block TCP traffic from a specific user on a multi-user system during 9:00PM and 5:00AM |
(B) Possible because it is network layer protocol.
(C) Possible because SP address is present in Network layer.
(D) Not possible, because to block specific user, we need user id which is present in Application layer.
Question 11 |
Using public key cryptography, X adds a digital signature to message M, encrypts <M, σ>, and sends it to Y, where it is decrypted. Which one of the following sequences of keys is used for the operations?
Encryption: X’s private key followed by Y’s private key; Decryption: X’s public key followed by Y’s public key | |
Encryption: X’s private key followed by Y’s public key; Decryption: X’s public key followed by Y’s private key | |
Encryption: X’s public key followed by Y’s private key; Decryption: Y’s public key followed by X’s private key | |
Encryption: X’s private key followed by Y’s public key; Decryption: Y’s private key followed by X’s public key |
Encryption: Source has to encrypt with its private key for forming Digital signature for Authentication. Source has to encrypt the (M, σ) with Y’s public key to send it confidentially.
Decryption: Destination Y has to decrypt first with its private key, then decrypt using source public key.
Question 12 |
Considering the following key using a block of five characters, encryption of the message "NETWORKING" using the Transposition Cipher is:
Plaintext : 5 4 3 2 1
Ciphertext 1 2 3 4 5
GNIKROWTEN | |
OGWNTIEKNR | |
OWTENGNIKR | |
NREKTIWNOG |
→According to given question ,
→Plaintext : 5 4 3 2 1
→Ciphertext 1 2 3 4 5
→Given message "NETWO RKING".
→The message is divided into two equal messages of 5 characters length.
→According to cipher text, The reverse of 5 characters of message is OWTEN GNIKR
Question 13 |
Consider an information exchange scenario where Anthony is the sender and Bond is the intended recipient of the data.
Match the following appropriately.
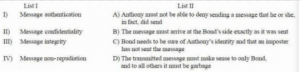
I-C, II-B, III-D, IV-A | |
I-C, II-D, III-A, IV-B | |
I-C, II-D, III-B, IV-A | |
I-A, II-D, III-B, IV-C |
Message confidentiality: The transmitted message must make sense to only bond and to all others it must be garbage.
Message Integrity: The message must arrive at the bond’s side exactly as it was sent. Message Non Repudiation: Anthony must not be able to deny sending a message that he or she in fact, did send
Options C is correct.
Question 14 |
Both Statement I and Statement II are true | |
Both Statement I and Statement II are false | |
Statement I is correct but Statement II is false | |
Statement I is incorrect but Statement II is true |
Diffie–Hellman key exchange is a method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as conceived by Ralph Merkle and named after Whitfield Diffie and Martin Hellman
Question 15 |
(A), (B) and (C) only | |
(B) and (E) only | |
(C) and (D) only | |
(A), (B), (C), (D) and (E) only |
Packets may be filtered by source and destination IP addresses, protocol, source and destination ports. The bulk of Internet communication in 20th and early 21st century used either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) in conjunction with well-known ports, enabling firewalls of that era to distinguish between specific types of traffic such as web browsing, remote printing, email transmission, file transfer.
Question 16 |
POP Server | |
Database Server | |
Proxy Server | |
Mail Server |
Question 17 |

Using ‘Z’ as bogus character.
TAXERTZENZ | |
EXTRANETZZ | |
EZXZTRZANZET | |
EXTZRANZETZ |
-- Plain text Message= EXTRANET
-- Bogus character=Z
-- Encrypt plain text message using Transposition cipher=?

Question 18 |
“TINESAX / EOAHTFX / HTLTHEY / MAIIAIX / TAPNGDL / OSTNHMX” | |
“TINESAX / EOAHTFX / MAIIAIX / HTLTHEY / TAPNGDL / OS TN HMX” | |
“TINESAX / EOAHTFX / HTLTHEY / MAIIAIX / OSTNHMX / TAPNGDL” | |
“EOAHTFX / TINESAX / HTLTHEY / MIIAIX / TAPNGDL / OSTNHMX” |
encrypt the message "The tomato is a plant in the nightshade family" using the keyword tomato. We get the grid given below.
We have written the keyword above the grid of the plaintext, and also the numbers telling us which order to read the columns in. Notice that the first "O" is 3 and the second "O" is 4, and the same thing for the two "T"s.

The plaintext is written in a grid beneath the keyword. The numbers represent the alphabetical order of the keyword, and so the order in which the columns will be read.
Starting with the column headed by "A", our ciphertext begins "TINESAX" from this column. We now move to the column headed by "M", and so on through the letters of the keyword in alphabetical order to get the ciphertext "TINESAX / EOAHTFX / HTLTHEY / MAIIAIX / TAPNGDL / OSTNHMX" (where the / tells you where a new column starts). The final ciphertext is thus "TINESAX EOAHTFX HTLTHEY MAIIAIX TAPNGDL OSTNHMX".
Question 19 |
Large changes in cipher text when the keyword is changed minimally | |
Large changes in cipher text when the plain text is changed | |
Large impact of keyword change to the length of the cipher text | |
None of the above |
Question 20 |
substitution | |
transposition | |
substitution and transposition | |
normalization |
Question 21 |
End-to-end encryption | |
Link encryption | |
Combination of both link and end-to-end encryption | |
Either link encryption or end-to-end encryption but not both |
Question 22 |
SHA-1 is used to generate hash code of message | |
The hash code is prepended to the message and sent to the receiver | |
The receiver uses RSA with senders public key to decrypt and recovered code | |
Receiver generates a new hash code for the message and compares with the recovered code and accept the message as authentic, if only, they match |
Question 23 |
RSA | |
Diffie-Hellman key exchange | |
Advanced Encryption Standard (AES) | |
Elliptic Curve Cryptography (ECC) |
Diffie-Hellman key exchange algorithm is not at all a encryption algorithm ,instead it is a key exchange algorithm.
AES is a secret key encryption algorithm.
Question 24 |
Circuit level gateways | |
Application level gateways | |
Packet filters | |
Digital Immune System |
Application level gateways is also a type of firewall. Packet filtering is a firewall technique used to control network access by monitoring outgoing and incoming packets and allowing them to pass or halt based on the source and destination Internet Protocol (IP) addresses, protocols and ports.
The Digital Immune system is a comprehensive approach to virus protection, and is not a type of firewall.
Question 25 |
A digital signature is
scanned signature
| |
signature in binary form
| |
encrypting information | |
handwritten signature
|
Question 26 |
A firewall is
an established network performance reference point
| |
software or hardware used to isolate a private network from a public network
| |
a virus that infects macros | |
a predefined encryption key used to encrypt and decrypt data transmissions |
