KVS DEC-2017
Question 1 |
Anti aliasing is important to improve readability of text. It deals with the
Elimination of "jaggies" | |
Spacing between two individual characters | |
Underlining letters | |
Spacing of a group of characters |
Question 1 Explanation:
● Antialiasing removes jagged edges by adding subtle color changes around the lines, tricking the human eye into thinking that the lines are not jagged.
● The slight changes in color around the edges of an image help the line blend around curves, giving the impression that the line is true.
● These color changes are made on a very small scale that the human eye cannot detect under normal circumstances. In order to be able to see that an image has been antialiased, it would have to be magnified.
● The slight changes in color around the edges of an image help the line blend around curves, giving the impression that the line is true.
● These color changes are made on a very small scale that the human eye cannot detect under normal circumstances. In order to be able to see that an image has been antialiased, it would have to be magnified.
Question 2 |
Consider a set of n tasks with known runtimes R1 ,R2 ,Rn , to be run uniprocessor machine. Which of the following processor scheduling algorithm will result in the maximum throughput?
Priority scheduling | |
Round robin | |
FCFS | |
SJF |
Question 2 Explanation:
→ In shortest job first scheduling algorithm, the processor selects the process with the smallest execution time to execute next.
→ SJF scheduling algorithm will result in the maximum throughput
→ SJF scheduling algorithm will result in the maximum throughput
Question 3 |
Which of the following is the appropriate format for graphics that can be embedded within an internet document?
HTML | |
BMP | |
TIFF | |
GIF |
Question 3 Explanation:
Most web browsers (excluding text-only ones like Linux, Mosaic) can display only a handful of these formats inline. The format of about 90% of these files is binary.
1. Graphical interchange format - GIF
For line art (such as one- or two-color logos), simple drawings, animations, and basically any image that has no gradients or blends. GIF is also the best format when you want to display an image with a transparent background.
2. J oint Photographic Experts Group - JPEG
JPEG is the best format for colorful, complex images (such as photographs); images containing gradients or color blends; and any other images with millions of colors.
3. Portable Network Graphics - PNG
PNG generally produces better-looking images with smaller file sizes than GIF for the same kinds of limited-color images. Really old browsers, such as IE 3, don’t support the PNG format, but most Web designers now choose this format over GIF because so few people use such old browser. Browsers as recent as IE6 don’t display transparent PNG files properly, which is unfortunate because PNG files tend to handle transparency better.
4. X-Bitmap/X-Pixelmap
X-Bitmaps are a common format on UNIX platforms, and are often found in older image and icon libraries. Here, a bit is used to represent each pixel of the graphics. Consequently, only black and white images are supported. Transparency is possible as in GIF since the white portion is treated as the color of the underlying background (making way for attractive designs). X-Pixel map is the colour equivalent of X-Bitmap. Here, 8 bits represent each pixel(256 colours). Obviously, both methods are very inefficient in terms of storage space required. It is quite uncommon outside the UNIX environment.
1. Graphical interchange format - GIF
For line art (such as one- or two-color logos), simple drawings, animations, and basically any image that has no gradients or blends. GIF is also the best format when you want to display an image with a transparent background.
2. J oint Photographic Experts Group - JPEG
JPEG is the best format for colorful, complex images (such as photographs); images containing gradients or color blends; and any other images with millions of colors.
3. Portable Network Graphics - PNG
PNG generally produces better-looking images with smaller file sizes than GIF for the same kinds of limited-color images. Really old browsers, such as IE 3, don’t support the PNG format, but most Web designers now choose this format over GIF because so few people use such old browser. Browsers as recent as IE6 don’t display transparent PNG files properly, which is unfortunate because PNG files tend to handle transparency better.
4. X-Bitmap/X-Pixelmap
X-Bitmaps are a common format on UNIX platforms, and are often found in older image and icon libraries. Here, a bit is used to represent each pixel of the graphics. Consequently, only black and white images are supported. Transparency is possible as in GIF since the white portion is treated as the color of the underlying background (making way for attractive designs). X-Pixel map is the colour equivalent of X-Bitmap. Here, 8 bits represent each pixel(256 colours). Obviously, both methods are very inefficient in terms of storage space required. It is quite uncommon outside the UNIX environment.
Question 4 |
Which of the following is true to declare variable of ASP?
Var | |
Dim | |
S | |
Set |
Question 4 Explanation:
We can declare VBScript variables with the Dim, Public or the Private statement.
Syntax: Dim variable_name
Example: Dim anand
Syntax: Dim variable_name
Example: Dim anand
Question 5 |
In the context of visual basic, multiple controls of the same type can be grouped into an array, in the same manner as a collection of data items. Such a grouping is known as
Control array | |
Primary array | |
Secondary array | |
An integer array |
Question 5 Explanation:
A control array is a group of controls that share the same name type and the same event procedures. Adding controls with control arrays uses fewer resources than adding multiple control of same type at design time.
A control array can be created only at design time, and at the very minimum at least one control must belong to it.
Features:
1. Controls that belong to the same control array share the same set of event procedures; this often dramatically reduces the amount of code you have to write to respond to a user's actions.
2. We can dynamically add new elements to a control array at run time; in other words, you can effectively create new controls that didn't exist at design time.
3. Elements of control arrays consume fewer resources than regular controls and tend to produce smaller executables. Besides, Visual Basic forms can host up to 256 different control names, but a control array counts as one against this number. In other words, control arrays let you effectively overcome this limit.
A control array can be created only at design time, and at the very minimum at least one control must belong to it.
Features:
1. Controls that belong to the same control array share the same set of event procedures; this often dramatically reduces the amount of code you have to write to respond to a user's actions.
2. We can dynamically add new elements to a control array at run time; in other words, you can effectively create new controls that didn't exist at design time.
3. Elements of control arrays consume fewer resources than regular controls and tend to produce smaller executables. Besides, Visual Basic forms can host up to 256 different control names, but a control array counts as one against this number. In other words, control arrays let you effectively overcome this limit.
Question 6 |
Consider two database relations R and S having 3 tuples in R and 2 tuples in S. What is the maximum number of tuples that could appear in the natural join of R and S?
6 | |
2 | |
3 | |
5 |
Question 6 Explanation:
→ If the tables R and S contains common attributes and value of that attribute in each tuple in both tables are same, then the natural join will result n*m tuples as it will return all combinations of tuples.
Consider following two tables

→ Result of natural join R * S (If domain of attribute C in the two tables are same )
→ You can see both R and S contain the attribute C whose value is 2 in each and every tuple. Table R contains 3 tuples, Table S contains 2 tuples, where Result table contains 3*2=6 tuples.
Note: While performing a natural join, if there were no common attributes between the two relations, Natural join will behave as Cartesian Product.
Consider following two tables

→ Result of natural join R * S (If domain of attribute C in the two tables are same )
→ You can see both R and S contain the attribute C whose value is 2 in each and every tuple. Table R contains 3 tuples, Table S contains 2 tuples, where Result table contains 3*2=6 tuples.
Note: While performing a natural join, if there were no common attributes between the two relations, Natural join will behave as Cartesian Product.
Question 7 |
Which of the following protocol is used for transferring electronic mail messages from one machine to another?
HTTP | |
FTP | |
SMTP | |
SNMP |
Question 7 Explanation:
→ Mail servers and other mail transfer agents use SMTP to send and receive mail messages on TCP port 25.
→ SMTP (Simple Mail Transfer Protocol) is a TCP/IP protocol used in sending and receiving e-mail.
→ However, since it is limited in its ability to queue messages at the receiving end, it is usually used with one of two other protocols, POP3 or IMAP, that let the user save messages in a server mailbox and download them periodically from the server.
→ In other words, users typically use a program that uses SMTP for sending e-mail and either POP3 or IMAP for receiving email.
→ SMTP (Simple Mail Transfer Protocol) is a TCP/IP protocol used in sending and receiving e-mail.
→ However, since it is limited in its ability to queue messages at the receiving end, it is usually used with one of two other protocols, POP3 or IMAP, that let the user save messages in a server mailbox and download them periodically from the server.
→ In other words, users typically use a program that uses SMTP for sending e-mail and either POP3 or IMAP for receiving email.
Question 8 |
OLE, a microsoft's component document technology, means
Overlay linking and exchange | |
Online linking and embedding | |
Open learning exchange | |
Object linking and embedding |
Question 8 Explanation:
→ Object Linking & Embedding (OLE) is a proprietary technology developed by Microsoft that allows embedding and linking to documents and other objects.
→ For developers, it brought OLE Control Extension (OCX), a way to develop and use custom user interface elements. On a technical level, an OLE object is any object that implements the IOleObject interface, possibly along with a wide range of other interfaces, depending on the object's needs.
Question 9 |
The problem of indefinite blockage of low priority jobs in general priority scheduling algorithm can be solved using
Swapping | |
Dirty bit | |
Aging | |
Compaction |
Question 9 Explanation:
→ Ageing is a scheduling technique used to avoid starvation. Fixed priority scheduling is a scheduling discipline, in which tasks queued for utilizing a system resource are assigned a priority each.
→ A task with a high priority is allowed to access a specific system resource before a task with a lower priority is allowed to do the same.
→ A disadvantage of this approach is that tasks assigned with a lower priority may be starved when a large number of high priority tasks are queued. Aging is used to gradually increase the priority of a task, based on its waiting time in the ready queue.
→ A task with a high priority is allowed to access a specific system resource before a task with a lower priority is allowed to do the same.
→ A disadvantage of this approach is that tasks assigned with a lower priority may be starved when a large number of high priority tasks are queued. Aging is used to gradually increase the priority of a task, based on its waiting time in the ready queue.
Question 10 |
What result set is returned from the following SQL query?
SELECT customer_name, telephone FROM customers
WHERE city IN('Jaipur','Delhi','Agra');
SELECT customer_name, telephone FROM customers
WHERE city IN('Jaipur','Delhi','Agra');
The cusomer_name of all customers who are not living IN Jaipur,Delhi OR Agra | |
The customer_name and telephone of all customers | |
The customer_name and telephone of all customers living IN either Jaipur,Delhi OR
Agra | |
The customer_name and telephone of all customers living IN Jaipur,Delhi AND Agra |
Question 10 Explanation:
Only logic here is, when we are using keyword IN there must be OR keyword.
Question 11 |
Which of the following data structures is most suitable for evaluating postfix expressions?
Tree | |
Stack | |
Linked List | |
Queue |
Question 11 Explanation:
Postfix Expression are usually converted from infix Expression using Stack Data structure.
Algorithm
We have Postfix[ ] Array, Stack, Infix[ ] Array
1. Scan the given expression (Infix ) from Left to Right [ one character at a time].
2. Check Whether the given character is an operator [+, -, *, /, ^ etc] or operand.
3. If it is an operand, then copy it in the Prefix Array.
4. If it is a operator then,
1. Check whether, Stack is empty or not
2. If it is empty then, push the operator in the stack and go to step
3. If Stack is not empty then compare the precedence of Top of stack with operator.
4. If the Top of Stack has higher or equal precedence then pop it and copy in the postfix array.
5. If the operator has higher precedence, push it in the stack and go to step 5.
6. If Stack is not empty go back to step 4(1).
5. Continue solving the expression in usual manner until the expression come to end.
6. Pop the remaining operand in the stack and copy it to postfix array.
Algorithm
We have Postfix[ ] Array, Stack, Infix[ ] Array
1. Scan the given expression (Infix ) from Left to Right [ one character at a time].
2. Check Whether the given character is an operator [+, -, *, /, ^ etc] or operand.
3. If it is an operand, then copy it in the Prefix Array.
4. If it is a operator then,
1. Check whether, Stack is empty or not
2. If it is empty then, push the operator in the stack and go to step
3. If Stack is not empty then compare the precedence of Top of stack with operator.
4. If the Top of Stack has higher or equal precedence then pop it and copy in the postfix array.
5. If the operator has higher precedence, push it in the stack and go to step 5.
6. If Stack is not empty go back to step 4(1).
5. Continue solving the expression in usual manner until the expression come to end.
6. Pop the remaining operand in the stack and copy it to postfix array.
Question 12 |
The major goal of object oriented programming is
top down program development | |
Speed | |
User interface | |
Reuse |
Question 12 Explanation:
Languages that support object oriented programming typically use inheritance for code reuse and extensibility in the form of either classes or prototypes. Those that use classes support two main concepts:
1. Classes – the definitions for the data format and available procedures for a given type or class of object; may also contain data and procedures (known as class methods) themselves, i.e. classes contain the data members and member functions
2. Objects – instances of classes
1. Classes – the definitions for the data format and available procedures for a given type or class of object; may also contain data and procedures (known as class methods) themselves, i.e. classes contain the data members and member functions
2. Objects – instances of classes
Question 13 |
Which of the following is the default scripting language in Active server pages(ASP)?
JavaScript | |
PHP | |
HTML | |
VBScript |
Question 13 Explanation:
The default scripting language used for writing ASP is VBScript, although you can use other scripting languages like JScript (Microsoft's version of JavaScript).
Question 14 |
What is the bitrate for transmitting uncompressed 800x600 pixel color frame with 8 bits/pixel at 40 frames/Second?
1536 Mbps | |
2.4 Mbps | |
15.36 Mbps | |
153.6 Mbps |
Question 14 Explanation:
Step-1: Given data, Uncompressed pixel = 800*600
Step-2: Each of 8 bit = 800*600 *8
Step-3: Bit rate for transmitting = 800*600 *8 *40 =153600000 bits
Step-4: Here, they are given in Mbps. 153600000 bits =153.6Mbps
Step-2: Each of 8 bit = 800*600 *8
Step-3: Bit rate for transmitting = 800*600 *8 *40 =153600000 bits
Step-4: Here, they are given in Mbps. 153600000 bits =153.6Mbps
Question 15 |
Assume the C++ definitions: Class circle: public point which of the following is false?
'point' is the base class and 'circle' is the derived class | |
The colon(:) in the header of class definition indicates inheritance | |
The keyword 'public' indicates type of inheritance | |
All the public and protected members of class 'circle' are inherited as public and protected members respectively into class point. |
Question 15 Explanation:
True: point' is the base class and 'circle' is the derived class
True: The colon(:) in the header of class definition indicates inheritance
True: The keyword 'public' indicates type of inheritance
False: All the public and protected members of class 'circle' are inherited as public and protected members respectively into class point.
True: The colon(:) in the header of class definition indicates inheritance
True: The keyword 'public' indicates type of inheritance
False: All the public and protected members of class 'circle' are inherited as public and protected members respectively into class point.
Question 16 |
Which of the following java statement declare and allocate a 2-dimensional array integers with four rows and five columns?
int array[ ] [ ]=new int [5][4]; | |
int array [4][5]; | |
int array[5][4]; | |
int array[ ] [ ]=new int[4][5]; |
Question 16 Explanation:
→ In question they are clearly mentioned that 4 rows and 5 columns.
→ Syntax int array[ ] [ ]=new int[row size][column size];
(or)
int[ ] [ ] array=new int[row size][column size];
So, Option D is correct answer.
→ Syntax int array[ ] [ ]=new int[row size][column size];
(or)
int[ ] [ ] array=new int[row size][column size];
So, Option D is correct answer.
Question 17 |
The technology that stores only the essential instructions on a microprocessor chip and thus enhances its speed is referred to as
MIMD | |
CISC | |
RISC | |
SIMD |
Question 17 Explanation:
A reduced instruction set computer(or)RISC is one whose instruction set architecture (ISA) allows it to have fewer cycles per instruction (CPI) than a complex instruction set computer (CISC).
Question 18 |
Ten signals, each requiring 3000 hz, are multiplexed onto a single channel using FDM. How much minimum bandwidth is required for the multiplexed channel? Assume that the guard bands are 300 Hz wide.
33,700 | |
30,000 | |
32,700 | |
33,000 |
Question 18 Explanation:
Step-1: Given data, 10 signals. Each signal requires 3000. So, 10*3000=30000 Hz
Step-2: Guard band (or gaps)=(10-9)=9.
300x9 =2700 Kz
Step-3: Minimum bandwidth is required for the multiplexed channel 30000+2700= 32700Hz
Step-2: Guard band (or gaps)=(10-9)=9.
300x9 =2700 Kz
Step-3: Minimum bandwidth is required for the multiplexed channel 30000+2700= 32700Hz
Question 19 |
Which of the following methods in JavaScript will display a window having a dialog box with a specific message, along with an OK and a CANCEL button as options?
prompt() | |
alert() | |
confirm() | |
request() |
Question 19 Explanation:
confirm(): Displays a dialog box with a message and an OK and a Cancel button
alert(): Displays an alert box with a message and an OK button
prompt(): Displays a dialog box that prompts the visitor for input
alert(): Displays an alert box with a message and an OK button
prompt(): Displays a dialog box that prompts the visitor for input
Question 20 |
To declare the version of XML, the correct syntax is
< / xml version='1.0'/ > | |
< ? xml version=”1.0”/ > | |
< *xml version='1.0'/ > | |
< ?xml version=*1.0*/ > |
Question 20 Explanation:
This line is called the XML prolog:
→ The XML prolog is optional. If it exists, it must come first in the document.
→ XML documents can contain international characters, like Norwegian øæå or French êèé.
→ To avoid errors, you should specify the encoding used, or save your XML files as UTF-8.
→ UTF-8 is the default character encoding for XML documents.
→ The XML prolog is optional. If it exists, it must come first in the document.
→ XML documents can contain international characters, like Norwegian øæå or French êèé.
→ To avoid errors, you should specify the encoding used, or save your XML files as UTF-8.
→ UTF-8 is the default character encoding for XML documents.
Question 21 |
Which of the following statements best describes the main reasons for normalising relational database?
(i) To achieve physical data independence
(ii) To remove data anomalies (insertion,update,delete,anomalies)
(iii) To save space on disk.
(i) To achieve physical data independence
(ii) To remove data anomalies (insertion,update,delete,anomalies)
(iii) To save space on disk.
(i),(ii) and (iii) | |
(i) and (ii) | |
(i) and (iii) | |
(ii) and (iii) |
Question 21 Explanation:
Normalising relational database reasons are
1. To remove data anomalies (insertion,update,delete,anomalies)
2. To save space on disk(It happens because of avoiding redundancy)
1. To remove data anomalies (insertion,update,delete,anomalies)
2. To save space on disk(It happens because of avoiding redundancy)
Question 22 |
A Thread is also called
a scheduler | |
a virtual process | |
a heavyweight process | |
a lightweight process |
Question 22 Explanation:
→ A light-weight process (LWP) is a means of achieving multitasking.
→ A LWP runs in user space on top of a single kernel thread and shares its address space and system resources with other LWPs within the same process. Multiple user level threads, managed by a thread library, can be placed on top of one or many LWPs - allowing multitasking to be done at the user level, which can have some performance benefits.
→ A LWP runs in user space on top of a single kernel thread and shares its address space and system resources with other LWPs within the same process. Multiple user level threads, managed by a thread library, can be placed on top of one or many LWPs - allowing multitasking to be done at the user level, which can have some performance benefits.
Question 23 |
Copying a process from memory to disk to allow space for other processes is called___
Demand paging | |
Deadlock | |
page fault | |
Swapping |
Question 23 Explanation:
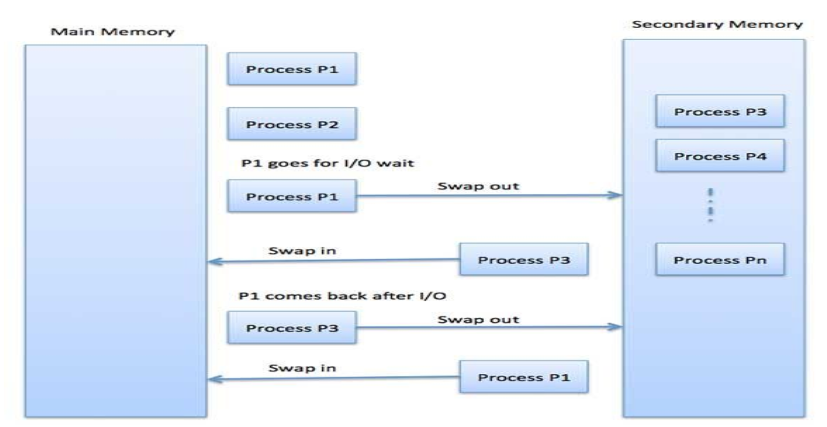
→ Swapping is a mechanism in which a process can be swapped temporarily out of main memory (or move) to secondary storage (disk) and make that memory available to other processes. At some later time, the system swaps back the process from the secondary storage to main memory.
→ The performance is usually affected by swapping process but it helps in running multiple and big processes in parallel and that's the reason Swapping is also known as a technique for memory compaction.
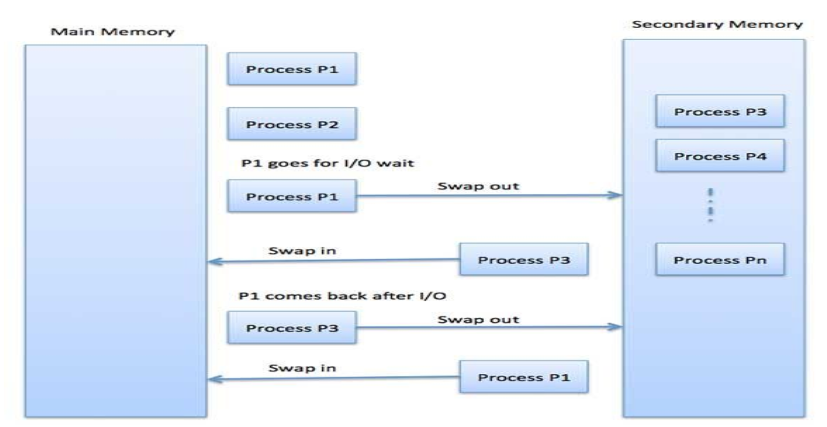
→ The performance is usually affected by swapping process but it helps in running multiple and big processes in parallel and that's the reason Swapping is also known as a technique for memory compaction.
Question 24 |
When a subroutine is called, the add the instruction following the instruction stored in/on the____
Program counter | |
Stack | |
Stack pointer | |
accumulator |
Question 24 Explanation:
The Program Counter is incremented after fetching an instruction, and holds the memory address of ("points to") the next instruction that would be executed.
Question 25 |
Consider the following code segment
if(Y<0)
{
X=-X;
Y=-Y;
}
Z=0;
while(Y>0)
{
Z=Z+X;
Y=Y-1;
}
Assume that X,Y and Z are integer variables, and that X and Y have be initialized. Which of the following best describes what this code segment does?
if(Y<0)
{
X=-X;
Y=-Y;
}
Z=0;
while(Y>0)
{
Z=Z+X;
Y=Y-1;
}
Assume that X,Y and Z are integer variables, and that X and Y have be initialized. Which of the following best describes what this code segment does?
Sets Z to be the product X*Y | |
Sets Z to be the sum X+Y | |
Sets Z to be the absolute value of Y | |
Sets Z to be the value of Y |
Question 25 Explanation:
Assume X=3 and Y=3
So, it satisfying condition while(Y>0)
Iteration-1: while(3>0)
Z=0+3⇒ Z=3
Y=3-1⇒ Y=2
Iteration-2: while(2>0)
Z=3+3=6
Y=2-1=1
Iteration-3:while(1>0)
Z=6+3
Y=1-1=0
Iteration-4 while(0>0) fails.
So,It Sets Z to be the product X*Y=3*3=9
So, it satisfying condition while(Y>0)
Iteration-1: while(3>0)
Z=0+3⇒ Z=3
Y=3-1⇒ Y=2
Iteration-2: while(2>0)
Z=3+3=6
Y=2-1=1
Iteration-3:while(1>0)
Z=6+3
Y=1-1=0
Iteration-4 while(0>0) fails.
So,It Sets Z to be the product X*Y=3*3=9
There are 25 questions to complete.
