UGC NET CS 2013 June-paper-2
Question 1 |
COCOMO stands for
COmposite COst MOdel | |
COnstructive COst MOdel | |
COnstructive Composite MOdel | |
COmprehensive Construction MOdel |
Question 1 Explanation:
COCOMO stands for COnstructive COst MOdel. It is a procedural software cost estimation model but not software process model. Linear sequential,prototype and spiral models are software process models.
The basic COCOMO equations take the form
1. Effort Applied (E) = a(KLOC)b [ man-months ]
2. Development Time (D) = c(Effort Applied)d [months]
3. People required (P) = Effort Applied / Development Time [count]
The basic COCOMO equations take the form
1. Effort Applied (E) = a(KLOC)b [ man-months ]
2. Development Time (D) = c(Effort Applied)d [months]
3. People required (P) = Effort Applied / Development Time [count]
Question 2 |
Match the following :


a-iii, b-ii, c-iv, d-i | |
a-ii, b-iii, c-iv, d-i | |
a-i, b-ii, c-iv, d-iii | |
a-i, b-ii, c-iii, d-iv |
Question 2 Explanation:
Good quality→ Meets both functional and non-functional requirements
Correctness→ Meets the functional requirements
Predictable→ Process is under statistical control
Reliable→ Program does not fail for a specified time in a given environment
Correctness→ Meets the functional requirements
Predictable→ Process is under statistical control
Reliable→ Program does not fail for a specified time in a given environment
Question 3 |
While estimating the cost of software, Lines Of Code(LOC) and Function Points(FP) are used to measure which one of the following ?
Length of code | |
Size of software | |
Functionality of software | |
None of the above |
Question 3 Explanation:
→ A function point is a "unit of measurement" to express the amount of business functionality an information system (as a product) provides to a user. Function points are used to compute a functional size measurement (FSM) of software. The cost (in dollars or hours) of a single unit is calculated from past projects.
→ Lines of code (LOC) is a software metric used to measure the size of a computer program by counting the number of lines in the text of the program's source code.
→ Lines of code (LOC) is a software metric used to measure the size of a computer program by counting the number of lines in the text of the program's source code.
Question 4 |
A good software design must have
High module coupling, High module cohesion | |
High module coupling, Low module cohesion | |
Low module coupling, High module cohesion | |
Low module coupling, Low module cohesion |
Question 4 Explanation:
→ A good software design must have low module coupling and high module cohesion.
→ Coupling and Cohesion are used in software design. Cohesion measures strength of a module while coupling measures interdependency between modules.
→ Coupling and Cohesion are used in software design. Cohesion measures strength of a module while coupling measures interdependency between modules.
Question 5 |
Cyclometric complexity of a flow graph G with n vertices and e edges is
V(G) = e+n–2 | |
V(G) = e–n+2 | |
V(G) = e+n+2 | |
V(G) = e–n–2 |
Question 5 Explanation:
Cyclomatic complexity uses 3 formulas:
1. The number of regions corresponds to the cyclomatic complexity
2. V(G),Flow graph is defined as V(G)=E-N+2 where E is the number of flow graph edges, and N is the number of flow graph nodes.
3. V(G),Flow graph is defined as V(G)=P+1 where p is the number of predicate nodes contained in the flow graph G.
1. The number of regions corresponds to the cyclomatic complexity
2. V(G),Flow graph is defined as V(G)=E-N+2 where E is the number of flow graph edges, and N is the number of flow graph nodes.
3. V(G),Flow graph is defined as V(G)=P+1 where p is the number of predicate nodes contained in the flow graph G.
Question 6 |
When the following code is executed what will be the value of x and y ?
int x = 1, y = 0;
y = x++;
2,1 | |
2,2 | |
1,1 | |
1,2 |
Question 6 Explanation:
Given post increment for x value. In post increment the value assign first and update after assigning.
So, x=2 and y=1
So, x=2 and y=1
Question 7 |
How many values can be held by an array A(–1,m;1,m) ?
m | |
m2 | |
m(m+1) | |
m(m+2) |
Question 7 Explanation:
int A[n] means "n" elements and index starts from 0 to n-1.
→ Similarly, int A[n][n] means both column and rows has "n" elements and total elements are n*n nothing but n2 elements.
In the given example ,an array A(-1,m;1,m)
→ In which rows indexes are -1,0,1,2, and so on up to m then total rows are "m+2".
→ columns consist of 1,2,3 and so on up to m then total elements in columns are "m".
Total elements are (m+2)*m
→ Similarly, int A[n][n] means both column and rows has "n" elements and total elements are n*n nothing but n2 elements.
In the given example ,an array A(-1,m;1,m)
→ In which rows indexes are -1,0,1,2, and so on up to m then total rows are "m+2".
→ columns consist of 1,2,3 and so on up to m then total elements in columns are "m".
Total elements are (m+2)*m
Question 8 |
What is the result of the expression (1&2)+(3/4) ?
1 | |
2 | |
3 | |
0 |
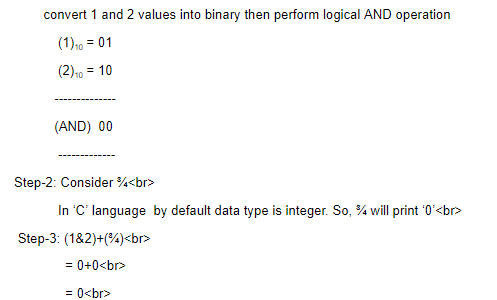
Question 8 Explanation:
Given statement, (1&2)+(3/4)
(1&2) means (1 AND 2)
(¾) means (3 divided by 4)
Step-1: First consider (1&2)
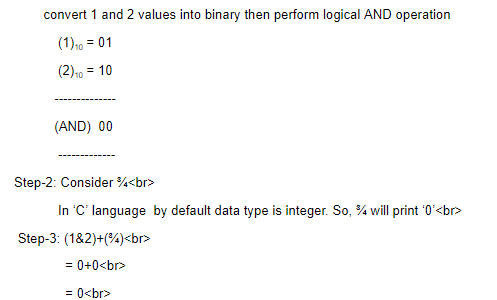
(1&2) means (1 AND 2)
(¾) means (3 divided by 4)
Step-1: First consider (1&2)
Question 9 |
How many times the word ‘print’ shall be printed by the following program segment ?
for (i=1, i≤2,i++)
for (j=1,j≤2,j++)
for(k=1,k≤2,k++)
printf("print/n")
for (i=1, i≤2,i++)
for (j=1,j≤2,j++)
for(k=1,k≤2,k++)
printf("print/n")
1 | |
3 | |
6 | |
8 |
Question 9 Explanation:
Iteration-1: In iteration-1 of ith loop will execute once and jth loop 2 times.
Each jth loop will execute kth loop 2 times.
Finally, iteration-1 will display 4 times of “print/n” word.
Iteration-2: In iteration-2 of ith loop will execute once and jth loop 2 times.
Each jth loop will execute kth loop 2 times.
Finally, iteration-2 will display 4 times of “print/n” word.
Above code segment will print 8 times.
Better understanding purpose given modified code segment:
#include
int main()
{
int i,j,k,jj=0,kk=0,ii=0;
for(i=1;i<=2;i++)
{
ii++;
for(j=1;j<=2;j++)
{
jj++;
for(k=1;k<=2;k++)
{
kk++;
printf("print/n");
}
}
}
printf("ii=%d \t jj=%d \t kk=%d",ii,jj,kk);
return 0;
}
Output:
print/n print/n print/n print/n print/n print/n print/n print/n
ii=2 jj=4 kk=8
Each jth loop will execute kth loop 2 times.
Finally, iteration-1 will display 4 times of “print/n” word.
Iteration-2: In iteration-2 of ith loop will execute once and jth loop 2 times.
Each jth loop will execute kth loop 2 times.
Finally, iteration-2 will display 4 times of “print/n” word.
Above code segment will print 8 times.
Better understanding purpose given modified code segment:
#include
int main()
{
int i,j,k,jj=0,kk=0,ii=0;
for(i=1;i<=2;i++)
{
ii++;
for(j=1;j<=2;j++)
{
jj++;
for(k=1;k<=2;k++)
{
kk++;
printf("print/n");
}
}
}
printf("ii=%d \t jj=%d \t kk=%d",ii,jj,kk);
return 0;
}
Output:
print/n print/n print/n print/n print/n print/n print/n print/n
ii=2 jj=4 kk=8
Question 10 |
Which of the following is not a type of Database Management System ?
Hierarchical | |
Network | |
Relational | |
Sequential |
Question 10 Explanation:
Most common types of database management system types are
1. Hierarchical databases
2. Network databases
3. Relational databases
4. Object-oriented databases
5. Graph databases
6. ER model databases
7. Document databases
1. Hierarchical databases
2. Network databases
3. Relational databases
4. Object-oriented databases
5. Graph databases
6. ER model databases
7. Document databases
Question 11 |
Manager’s salary details are to be hidden from Employee Table. This Technique is called as
Conceptual level Datahiding | |
Physical level Datahiding | |
External level Datahiding | |
Logical level Datahiding |
Question 11 Explanation:
1. Physical (or) Internal view is at the lowest level of abstraction, closest to the physical storage method used. It indicates how the data will be stored and describes the data structures and access methods to be used by the database. There is one internal view for the entire database.
2. Global or Conceptual View : At this level of abstraction all the database entities and the relationships among them are included. There is one conceptual view for the entire database.
3. External or User View: The external or user view is at the highest level of database abstraction where only those portions of the database concern to a user or application programme are included. Any number if external or user views may exists for a given global or conceptual view.

2. Global or Conceptual View : At this level of abstraction all the database entities and the relationships among them are included. There is one conceptual view for the entire database.
3. External or User View: The external or user view is at the highest level of database abstraction where only those portions of the database concern to a user or application programme are included. Any number if external or user views may exists for a given global or conceptual view.

Question 12 |
A Network Schema
restricts to one to many relationship | |
permits many to many relationship | |
stores Data in a Database | |
stores Data in a Relation |
Question 12 Explanation:
→ The network model expands upon the hierarchical structure, allowing many-to-many relationships in a tree-like structure that allows multiple parents. It was most popular before being replaced by the relational model, and is defined by the CODASYL specification.
→ The network model organizes data using two fundamental concepts, called records and sets.
→ Records contain fields (which may be organized hierarchically, as in the programming language COBOL).
→ Sets (not to be confused with mathematical sets) define one-to-many relationships between records: one owner, many members.
→ A record may be an owner in any number of sets, and a member in any number of sets.
→ The network model organizes data using two fundamental concepts, called records and sets.
→ Records contain fields (which may be organized hierarchically, as in the programming language COBOL).
→ Sets (not to be confused with mathematical sets) define one-to-many relationships between records: one owner, many members.
→ A record may be an owner in any number of sets, and a member in any number of sets.
There are 12 questions to complete.
