Data-Structures
Question 1 |
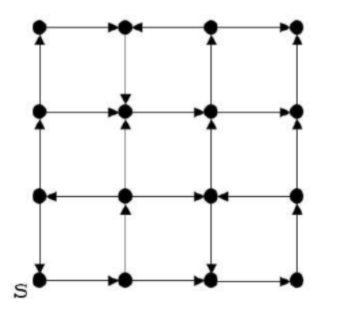
Which of the following is/are correct about the graph?
A | For each pair of vertices u and v, there is a directed path from u to v. |
B | The graph does not have a strongly connected component. |
C | The graph does not have a topological order. |
D | A depth-first traversal staring at vertex S classifies three directed edges as back edges. |
Option-1: FALSE: There is no path from top right corner vertex to any other vertex
Option-2: FALSE: A directed graph is called strongly connected if there is a path in each direction between each pair of vertices of the graph. As there is no path from the above vertex then this statement is wrong.
Option-3: TRUE: This graph does have directed cycles, thus topological order can not be possible for according to topological definition.

Question 2 |
A | 1 |
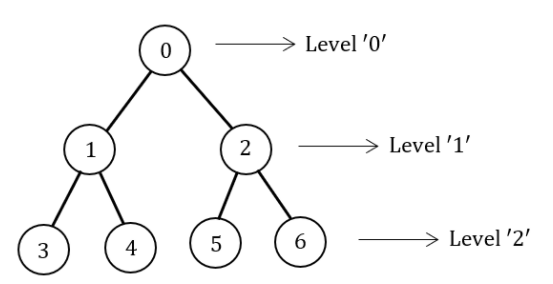
A={0,1,2} → BFS
The BFS traverse through level by level.
DFS:
B={0,1,3}
B={0,1,4}
B={0,2,6}
B={0,2,5}
The DFS starts at the root node (selecting some arbitrary node as the root node in the case of a graph) and explores as far as possible along each branch before backtracking.
|A-B| = 1
Note: The cardinality of set A-B is 1.
Question 3 |
#include<stdio.h>
#include<stdlib.h>
Struct Node{
int value;
struct Node *next;};
int main() {
struct Node *boxE, *head, *boxN; int index = 0;
boxE = head = (struct Node *) malloc(sizeof(struct Node));
head->value = index;
for (index = 1; index <= 3; index++) {
boxN = (struct Node *) malloc(sizeof(struct Node));
boxE->next = boxN;
boxN->value = index;
boxE = boxN; }
for (index = 0; index <= 3; index++) {
printf(“Value at index %d is %d\n”, index, head->value);
head = head->next;
printf(“Value at index %d is %d\n”, index+1, head->value); } }
Which one of the statements below is correct about the program?
A | Upon execution, the program creates a linked-list of five nodes. |
B | It dereferences an uninitialized pointer that may result in a run-time error. |
C | Upon execution, the program goes into an infinite loop. |
D | It has a missing return which will be reported as an error by the compiler. |
One node is created with value 0.
Loop i runs from 1 to 3. Hence total 4 nodes will be created.
0 → 1 → 2 → 3 → NULL
When index =3, head =3
Head = Head → Next
Head → Value from printf will generate an error.
Question 4 |
What is the number of binary trees with 3 nodes which when traversed in postorder give the sequence A, B, C? Draw all these binary trees.
A | Theory Explanation. |
Question 5 |
The preorder traversal of a binary search tree is 15, 10, 12, 11, 20, 18, 16, 19.
Which one of the following is the postorder traversal of the tree?
A | 20, 19, 18, 16, 15, 12, 11, 10 |
B | 11, 12, 10, 16, 19, 18, 20, 15
|
C | 10, 11, 12, 15, 16, 18, 19, 20 |
D | 19, 16, 18, 20, 11, 12, 10, 15 |
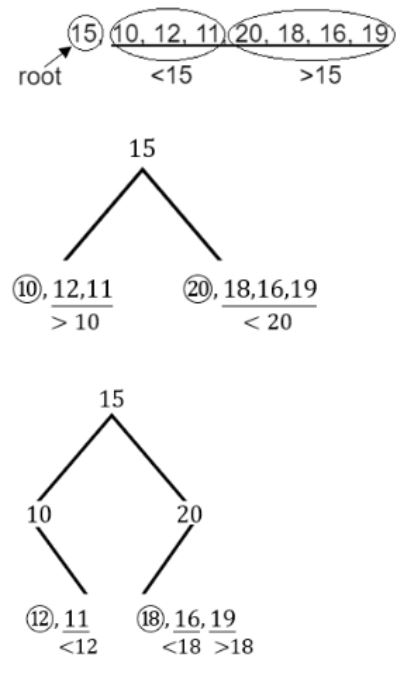

Postorder:
11, 12, 10, 16, 19, 18, 20, 15
Question 6 |
Consider a double hashing scheme in which the primary hash function is h1(k) = k mod 23, and the secondary hash function is h2(k) = 1 + (k mod 19). Assume that the table size is 23. Then the address returned by probe 1 in the probe sequence (assume that the probe sequence begins at probe 0) for key value k=90 is _______.
A | 13 |
• K=90
• h1(k) = k mod 23 = 90 mod 23 = 21
• In case of collision, we need to use secondary hash function.
• h2(k) = 1 + (k mod19) = 1 + 90mod19 = 1+14 = 15
• Now (21+15) mod 23 = 36 mod 23 = 13
• So the address is 13.
Question 7 |
What is the worst case time complexity of inserting n elements into an empty linked list, if the linked list needs to be maintained in sorted order?
A | θ(n log n) |
B | θ(n2) |
C | θ(1) |
D | θ(n) |
Total number of elements inserted into an empty linked list is O(n). So, it will take O(n) time in the worst case.
After inserting elements into an empty linked list we have to perform sorting operation.
To get minimum time complexity to perform sorting order is merge sort. It will give O(nlogn) time complexity only.
Let head be the first node of the linked list to be sorted and head Reference be the pointer to head.
The head in MergeSort as the below implementation changes next links to sort the linked lists (not data at the nodes), so head node has to be changed if the data at the original head is not the smallest value in the linked list.
Note: There are other sorting methods also will give decent time complexity but quicksort will give O(n2) and heap sort will not be suitable to apply.
Question 8 |
Consider the following C program.
#includeint main () { int a [4] [5] = {{1, 2, 3, 4, 5}, {6, 7, 8, 9, 10}, {11, 12, 13, 14, 15}, {16, 17, 18, 19, 20}}; printf (“%d\n”, *(*(a+**a+2) +3)); return (0); }
The output of the program is _______.
A | 19 |
#include
int main()
{
int a[4][5] = { {1,2,3,4,5},
{6,7,8,9,10},
{11,12,13,14,15},
{16,17,18,19,20}
};
printf("%d\n",a); //880 (consider base address = 880)
printf("%d\n",*a); //880
printf("%d\n",**a); //1
printf("%d\n",**a+2); //3
printf("%d\n",a+**a+2); //940
printf("%d\n",*(a+**a+2));//940
printf("%d\n",*(a+**a+2)+3);//952
printf("%d\n",*(*(a+**a+2)+3));//19
return 0;
}

Question 9 |
What is the worst case time complexity of inserting n2 elements into an AVL-tree with n elements initially?
A | θ(n4)
|
B | θ(n2)
|
C | θ(n3) |
D | θ(n2 log n) |
In question they asked about n2 elements.
So, In worst case it will take o(n2 log n) time.
Question 10 |
Let G = (V,E) be a directed, weighted graph with weight function w:E → R. For some function f:V → R, for each edge (u,v) ∈ E, define w'(u,v) as w(u,v) + f(u) - f(v).
Which one of the options completes the following sentence so that it is TRUE?
“The shortest paths in G under w are shortest paths under w’ too, _______”.
A | if and only if f(u) is the distance from s to u in the graph obtained by adding a new vertex s to G and edges of zero weight from s to every vertex of G |
B | if and only if ∀u ∈ V, f(u) is positive
|
C | if and only if ∀u ∈ V, f(u) is negative |
D | for every f: V→R |


Question 11 |
In a balanced binary search tree with n elements, what is the worst case time complexity of reporting all elements in range [a,b]? Assume that the number of reported elements is k.
A | θ(n log k) |
B | θ(log n + k) |
C | θ(k log n) |
D | θ(log n) |
Time complexity of the above program is O(h + k) where h is the height of BST and k is the number of nodes in a given range.
Here h is log n, hence O(log n+k).
Question 12 |
Consider the array representation of a binary min-heap containing 1023 elements. The minimum number of comparisons required to find the maximum in the heap is _______.
A | 511 |
n=1023
= Ceil(1023/2)
= 512
So, the maximum element is also part of n/2.
So, we have to subtract from the total elements
= 512-1
= 511
Question 13 |
Consider the following statements:
- (i) First-in-first out types of computations are efficiently supported by STACKS.
(ii) Implementing LISTS on linked lists is more efficient than implementing LISTS on an array for almost all the basic LIST operations.
(iii) Implementing QUEUES on a circular array is more efficient than implementing QUEUES on a linear array with two indices.
(iv) Last-in-first-out type of computations are efficiently supported by QUEUES.
Which of the following is correct?
A | (ii) and (iii) are true |
B | (i) and (ii) are true |
C | (iii) and (iv) are true |
D | (ii) and (iv) are true |
(iv) LIFO computation efficiently supported by stacks.
Then given (i) and (iv) are false.
Answer:- A
Question 14 |
An advantage of chained hash table (external hashing) over the open addressing scheme is
A | Worst case complexity of search operations is less? |
B | Space used is less |
C | Deletion is easier |
D | None of the above |
Question 15 |
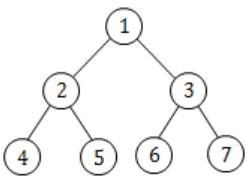
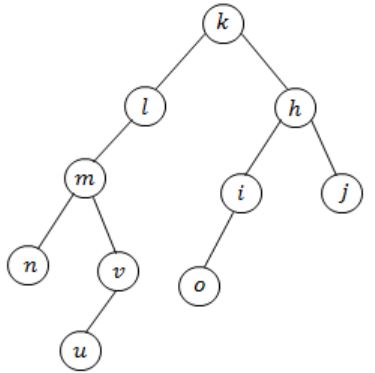
In the balanced binary tree in the below figure, how many nodes will become unbalanced when a node is inserted as a child of the node “g”?

A | 1 |
B | 3 |
C | 7 |
D | 8 |
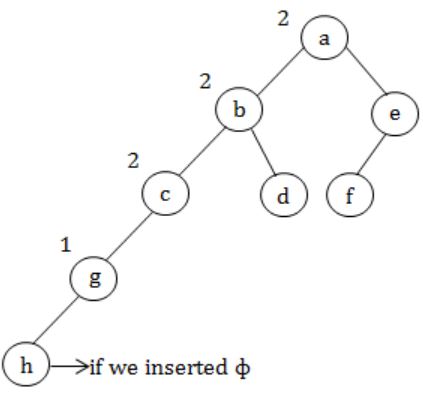
a, b, c are going to unbalance.
Question 16 |
Which of the following sequences denotes the post order traversal sequence of the tree of question 14?
A | f e g c d b a |
B | g c b d a f e |
C | g c d b f e a |
D | f e d g c b a |
Left → Right → Root
g c d b f e a
Question 17 |
The minimum number of interchanges needed to convert the array
89, 19, 40, 17, 12, 10, 2, 5, 7, 11, 6, 9, 70
into a heap with the maximum element at the root is
A | 0 |
B | 1 |
C | 2 |
D | 3 |

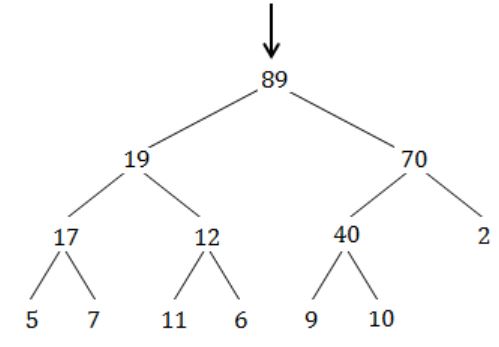
Question 18 |
A binary search tree is generated by inserting in order the following integers:
50, 15, 62, 5, 20, 58, 91, 3, 8, 37, 60, 24
The number of nodes in the left subtree and right subtree of the root respectively is
A | (4, 7) |
B | (7, 4) |
C | (8, 3) |
D | (3, 8) |
So greater than 50 will be in right subtree of 50 and less than 50 in left subtree.
So, answer will be (7, 4).
Question 19 |
A binary search tree is used to locate the number 43. Which of the following probe sequences are possible and which are not? Explain.
A | 61 52 14 17 40 43 |
B | 2 3 50 40 60 43 |
C | 10 65 31 48 37 43 |
D | 81 61 52 14 41 43 |
E | 17 77 27 66 18 43 |
Question 20 |
The concatenation of two lists is to be performed in O(1) time. Which of the following implementations of a list should be used?
A | Singly linked list |
B | Doubly linked list |
C | Circular doubly linked list |
D | Array implementation of list |
Question 21 |
Which of the following is essential for converting an infix expression to the postfix from efficiently?
A | An operator stack |
B | An operand stack |
C | An operand stack and an operator stack |
D | A parse tree |
An operand stack ⇒ Postfix to Prefix
Operator & operand stack ⇒ We don't use two stacks
Parse tree ⇒ No use
Question 22 |
A binary search tree contains the value 1, 2, 3, 4, 5, 6, 7, 8. The tree is traversed in pre-order and the values are printed out. Which of the following sequences is a valid output?
A | 5 3 1 2 4 7 8 6 |
B | 5 3 1 2 6 4 8 7 |
C | 5 3 2 4 1 6 7 8 |
D | 5 3 1 2 4 7 6 8 |
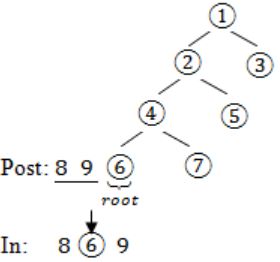
Option D:
Let draw binary search tree for the given sequence,
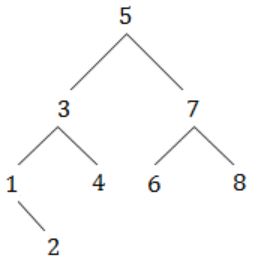
After traversing through this tree we will get same sequence.
Question 23 |
A priority queue Q is used to implement a stack that stores characters. PUSH (C) is implemented INSERT (Q, C, K) where K is an appropriate integer key chosen by the implementation. POP is implemented as DELETEMIN(Q). For a sequence of operations, the keys chosen are in
A | non-increasing order |
B | non-decreasing order |
C | strictly increasing order |
D | strictly decreasing order |
Question 24 |
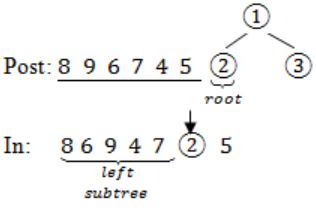
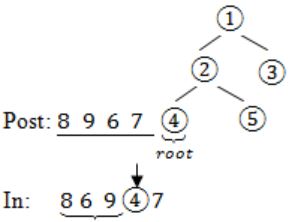
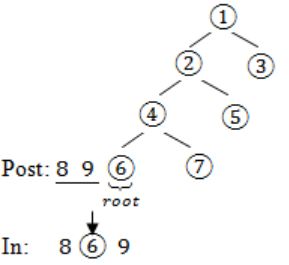
The postorder traversal of a binary tree is 8, 9, 6, 7, 4, 5, 2, 3, 1. The inorder traversal of the same tree is 8, 6, 9, 4, 7, 2, 5, 1, 3. The height of a tree is the length of the longest path from the root to any leaf. The height of the binary tree above is _______.
A | 1 |
B | 2 |
C | 3 |
D | 4 |
In – 8 6 9 4 7 2 5 1 3
Post: 8 9 6 7 4 5 2 3 1→(root)
In: 8 6 9 4 7 2 5→(left subtree) 13→(right subtree)
Question 25 |
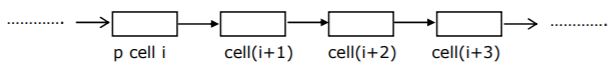
A queue is implemented using a non-circular singly linked list. The queue has a head pointer and a tail pointer, as shown in the figure. Let n denote the number of nodes in the queue. Let 'enqueue' be implemented by inserting a new node at the head, and 'dequeue' be implemented by deletion of a node from the tail.

Which one of the following is the time complexity of the most time-efficient implementation of 'enqueue' and 'dequeue, respectively, for this data structure?
A | θ(1), θ(1) |
B | θ(1), θ(n) |
C | θ(n), θ(1) |
D | θ(n), θ(n) |
But if we have pointer to the tail of the list in order to delete it, we need the address of the 2nd last node which can be obtained by traversing the list which takes O(n) time.
Question 26 |
(I) No edge of G is a cross edge with respect to TD.(A cross edge in G is between two nodes neither of which is an ancestor of the other in TD.)
(II) For every edge (u,v) of G, if u is at depth i and v is at depth j in TB, then ∣i−j∣ = 1.
Which of the statements above must necessarily be true?
A | I only |
B | II only |
C | Both I and II |
D | Neither I nor II |
II. Just draw a triangle ABC. Source is A. Vertex B and C are at same level at distance 1.
There is an edge between B and C too. So here |i - j| = |1 - 1| = 0. Hence, False.
Question 27 |
The number of possible min-heaps containing each value from {1, 2, 3, 4, 5, 6, 7} exactly once is ___________.
A | 80 |
B | 81 |
C | 82 |
D | 83 |
--> After sorting, pick the minimum element and make it the root of the min heap.
--> So, there is only 1 way to make the root of the min heap.
--> Now we are left with 6 elements
Question 28 |
Which of the following statements is false?
A | A tree with a n nodes has (n – 1) edges |
B | A labeled rooted binary tree can be uniquely constructed given its postorder and preorder traversal results |
C | A complete binary tree with n internal nodes has (n + 1) leaves |
D | Both B and C |
D: The maximum no. of nodes in a binary tree of height h is 2h+1 - 1.
h=2 ⇒ 23 - 1 ⇒ 7
Question 29 |
A complete n-ary tree is one in which every node has 0 or n sons. If x is the number of internal nodes of a complete n-ary tree, the number of leaves in it is given by
A | x(n-1) + 1 |
B | xn - 1 |
C | xn + 1 |
D | x(n+1) |
Let no. of leaf nodes = L
Let nt be total no. of nodes.
So, L+x = nt -----(I)
Also for n-ary tree with x no. of internal nodes, total no. of nodes is,
nx+1 = nt -----(II)
So, equating (I) & (II),
L+x = nx+1
L = x(n-1) + 1
Question 30 |
Let A be a two dimensional array declared as follows:
A: array [1 ... 10] [1 ... 15] of integer;
Assuming that each integer takes one memory location, the array is stored in row-major order and the first element of the array is stored at location 100, what is the address of the element a[i][j]?
A | 15i + j + 84 |
B | 15j + i + 84 |
C | 10i + j + 89 |
D | 10j + i + 89 |
100 + 15 * (i-1) + (j-1)
= 100 + 15i - 15 + j - 1
= 15i + j + 84
Question 31 |
Faster access to non-local variables is achieved using an array of pointers to activation records called a
A | stack |
B | heap |
C | display |
D | activation tree |
→ Use a pointer array to store the activation records along the static chain.
→ Fast access for non-local variables but may be complicated to maintain.
Question 32 |
Let p be a pointer as shown in the figure in a single linked list.
What do the following assignment statements achieve?
- q: = p → next
p → next:= q → next
q → next:=(q → next) → next
(p → next) → next:= q
(b) Compute the postfix equivalent of the following Infix expression
3 * log(x+1) - a/2
A | Theory Explanation. |
Question 33 |
Draw the binary tree with node labels a, b, c, d, e, f and g for which the inorder and postorder traversals result in the following sequences:
Inorder a f b c d g e Postorder a f c g e d b
A | Theory Explanation. |
Question 34 |
(a) Derive a recurrence relation of the size of the smallest AVL tree with height h.
(b) What is the size of the smallest AVL tree with height 8.A | Theory Explanation. |
Question 35 |
The number of articulation points of the following graph is

A | 0 |
B | 1 |
C | 2 |
D | 3 |
Total no. of articulation points = 3
Question 36 |
(a) In a binary tree, a nil node is defined to be a node with 2 children. Use induction on the height of the binary tree to prove that the number of full nodes plus one is equal to the number of leaves.
(b) Draw a min-heap that results from insertion of the following elements in order into an initially empty min-heap: 7, 6, 5, 4, 2, 3, 1. Show the result after the deletion of the root of this heap.
A | Theory Explanation. |
Question 37 |
The most appropriate matching for the following pairs
X: depth first search 1: heap
Y: breadth-first search 2: queue
Z: sorting 3: stack
is
A | X – 1 Y – 2 Z – 3 |
B | X – 3 Y – 1 Z – 2 |
C | X – 3 Y – 2 Z – 1 |
D | X – 2 Y – 3 Z – 1 |
Queue is used in breadth-first search.
Heap is used in heap.
Question 38 |
Consider the following nested representation of binary trees: (X Y Z) indicates Y and Z are the left and right sub stress, respectively, of node X. Note that Y and Z may be NULL, or further nested. Which of the following represents a valid binary tree?
A | (1 2 (4 5 6 7)) |
B | (1 (2 3 4) 5 6) 7) |
C | (1 (2 3 4) (5 6 7)) |
D | (1 (2 3 NULL) (4 5)) |

(Proper Representation)
Question 39 |
Suppose you are given an array s[1...n] and a procedure reverse (s,i,j) which reverses the order of elements in a between positions i and j (both inclusive). What does the following sequence do, where 1 ≤ k ≤ n:
reverse(s, 1, k) ;
reverse(s, k + 1, n);
reverse(s, l, n); A | Rotates s left by k positions |
B | Leaves s unchanged |
C | Reverses all elements of s |
D | None of the above |
Question 40 |
Let LASTPOST, LASTIN and LASTPRE denote the last vertex visited in a postorder, inorder and preorder traversal. Respectively, of a complete binary tree. Which of the following is always tree?
A | LASTIN = LASTPOST |
B | LASTIN = LASTPRE |
C | LASTPRE = LASTPOST |
D | None of the above |
But in case of complete binary last level need not to be full in that case LASTPRE is not equal to LASTIN.
Question 41 |
Let G be an undirected graph. Consider a depth-first traversal of G, and let T be the resulting depth-first search tree. Let u be a vertex in G and let ν be the first new (unvisited) vertex visited after visiting u in the traversal. Which of the following statements is always true?
A | {u, v} must be an edge in G, and u is a descendant of v in T |
B | {u, v} must be an edge in G, and v is a descendant of u in T |
C | If {u, v} is not an edge in G then u is a leaf in T |
D | If {u, v} is not an edge in G then u and v must have the same parent in T |
In DFS after visiting u, there is no child node then back tracking is happen and then visit the node v. There is no need of (u,v) be an edge.
Question 42 |
Suppose a stack implementation supports, in addition to PUSH and POP, an operation REVERSE, which reverses the order of the elements on the stack.
(a) To implement a queue using the above stack implementation, show how to implement ENQUEUE using a single operation and DEQUEUE using a sequence of 3 operations.
(b) The following postfix expression, containing single digit operands and arithmetic operators + and *, is evaluated using a stack.
5 2 * 3 4 + 5 2 * * +
Show the contents of the stack.
- (i) After evaluating 5 2 * 3 4 +
(ii) After evaluating 5 2 * 3 4 + 5 2
(iii) At the end of evaluation.
A | Theory Explanation is given below. |
Dequeue → reverse, pop, reverse
(b) (i) After evaluating 5 2 * 3 4 +
Sol:
7(3+4) 10(5*2)
(ii) After evaluating 5 2 * 3 4 + 5 2
Sol:
25(5*5) 7(3+4) 10(5*2)
(iii) At the end of evaluation
Sol: 80
Question 43 |
Suppose you are given arrays p[1…..N] and q[1…….N] both uninitialized that is, each location may contain an arbitrary value), and a variable count, initialized to 0. Consider the following procedures set and iset:
set (i) {
count = count + 1;
q [count] = i;
p[i] = count;
}
is_set(i) {
if (p[i] ≤ 0 or p[i] > count)
return false;
if (q[p[i]] ≠i)
return false;
return true;
}
(a) Suppose we make the following sequence of calls:
set (7); set (3); set(9);
After these quence of calls, what is the value of count, and what do q[1], q[2], q[3], p[7], p[3] and p[9] contain?
(b) Complete the following statement “The first count elements of _______ contain values i such that set (__________) has been called”.
(c) Show that if set (i) has not been called for some i, then regardless of what p[i] contains, is_set (i) will return false.
A | Theory Explanation is given below. |
then q[1] = 7; p[7] = 1
At set(3) ⇒ count = 2
then q[2] = 3; p[3] = 2
At set[9] ⇒ count = 3
then q[3] = 9; p[9] = 3;
(b) "The first count elements of array q contains value i such that set (i) has been called".
(c) If set(i) has not been celled for some i, then regardless of what p[i] contains, when we call is set(i) then
if (q[p[i]] ≠ i)
return false;
Will always execute, because if set(i) is not called then p[i]≠count(any) and for then same count q[count]≠i.
So if statement will be true and will return false.
Question 44 |
Consider any array representation of an n element binary heap where the elements are stored from index 1 to index n of the array. For the element stored at index i of the array (i≤n), the index of the parent is
A | i-1 |
B | ⌊i/2⌋ |
C | ⌈i/2⌉ |
D | (i+1)/2 |
Left Child is at index: 2i
Right child is at index: 2*i+1
Question 45 |
Consider an undirected unweighted graph G. Let a breadth-first traversal of G be done starting from a node r. Let d(r,u) and d(r,v) be the lengths of the shortest paths from r to u and v respectively in G. If u is visited before v during the breadth-first traversal, which of the following statements is correct?
A | d(r,u) |
B | d(r,u)>d(r,v) |
C | d(r,u)≤d(r,v) |
D | None of the above |
Question 46 |
What is the minimum number of stacks of size n required to implement a queue of size n?
A | One |
B | Two |
C | Three |
D | Four |
Question 47 |
Consider the following three C functions:
[PI] int*g(void)
{
int x = 10;
return(&x);
}
[P2] int*g(void)
{
int*px;
*px = 10;
return px;
}
[P3] int*g(void)
{
int*px;
px = (int *) malloc(sizeof(int));
*px = 10;
return px;
}
Which of the above three functions are likely to cause problems with pointers?
A | Only P3 |
B | Only P1 and P3 |
C | Only P1 and P2 |
D | P1, P2 and P3 |
[P2] → It will cause problem because px is in int pointer that is not assigned with any address and we are doing dereferencing.
[P3] → It will work because memory will be stored in px that can be use further. Once function execution completes this will exist in Heap.
Question 48 |
(a) Insert the following keys one by one into a binary search tree in the order specified.
15, 32, 20, 9, 3, 25, 12, 1
Show the final binary search tree after the insertions.
(b) Draw the binary search tree after deleting 15 from it.
(c) Complete the statements S1, S2 and S3 in the following function so that the function computes the depth of a binary rooted at t.
typedef struct tnode{
int key;
struct tnode *left, *right;
} *Tree;
int depth(Tree t)
{
int x,y;
it (t == NULL) return0;
x=depth(t → left);
S1: ____________;
S2: if(x>y) return _____________:
S3: else return _____________;
} A | Theory Explanation is given below. |
Question 49 |
A | log n |
B | n/2 |
C | (log2)n - 1 |
D | n |
Question 50 |
The results returned by function under value-result and reference parameter passing conventions
A | Do not differ |
B | Differ in the presence of loops |
C | Differ in all cases |
D | May differ in the presence of exception |
