JT(IT) 2018 PART-B Computer Science
Question 1 |
Which of the following numerical values is NOT a valid constant in C language?
12345L | |
018CDF
| |
9.3e12 | |
0XBCF
|
→ 018CDF starts with 0 means octal number but actually we are given decimal and hexa numbers. So it is not a valid constant.
→ 9.3e12 float number
→ 0XBCF is hexa number. Valid constant.
Question 2 |
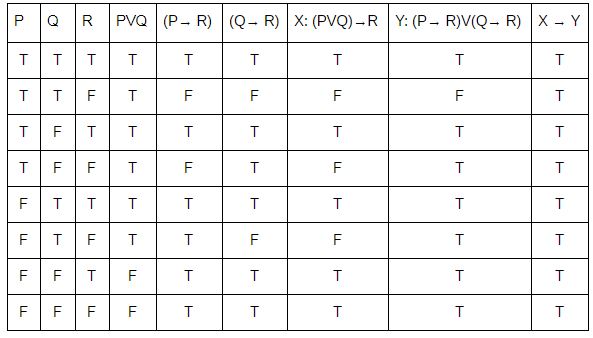
Let P, Q and R be three atomic prepositional assertions, and
- X : (P ∨ Q) → R
Y : (P → R) ∨ (Q → R)
Which one of the following is a tautology?
X → Y
| |
Y → X | |
X ≣ Y | |
~Y → X
|
Question 3 |
Which of the following is NOT a symmetric key algorithm?
Ellipse Curve Cryptography
| |
Advanced Encryption standard
| |
Data Encryption Standard
| |
Blowfish |

Question 4 |
Which of the following statements is FALSE?
The long term scheduler controls the degree of multiprogramming
| |
Multiple process of a single program cannot exist | |
Ready queue of the processes resides in main memory
| |
A process can have multiple sub processes
|
→ Ready queue of the processes resides in main memory.
→ A process can have multiple sub processes.
→ Multiple process of a single program cannot exist because each program can have only one process.
Question 5 |
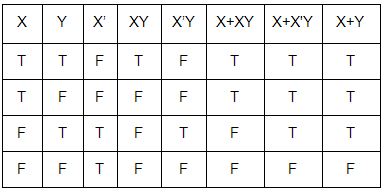
Which of the following Boolean equations is/are correct?
X(X'+ Y) = XY' X + XY = X X + X'Y = X + Y
only (iii) | |
only (ii)
| |
only (i) | |
Both (ii) and (iii)
|
Question 6 |
With respect to compiler design, "recursive descent" is a ____ parsing technique that reads the inputs from ____.
top-down, right to left
| |
top-down, left to right
| |
bottom up, right to left | |
bottom up, left to right
|
→ Top down parsers reads the input from left to right and bottom up parsers are reads the input from left to right and reverse.
Question 7 |
Which of the following statements is/are FALSE?
- (i) XML element names are case sensitive
(ii) In XML, empty element can be represented as
(iii) XML element names can contain spaces
only (iii) | |
only (ii) and (iii)
| |
only (i) and (iii)
| |
only (ii)
|
1. text
2. attributes
3. other elements or a mix of the above
Note: XML element names cannot contain spaces.
Question 8 |
For what values of k, the points(-k+1, 2k),(k, 2-2K) and (-4-k, 6-2k) are collinear?
0, 1
| |
-1, 1 | |
-1, 1/2
| |
1/2, -1/2
|
1/2[X1(Y2 - Y3) + X2(Y3 - Y1) + X3(Y1 - Y2)] = 0
Here, X1 = -k + 1, Y1 = 2k, X2 = k, Y2 = 2 – 2k, X3 = -4 - k, Y3 = 6 – 2k
1/2[-k + 1(2 – 2k - 6 + 2k) + k(6 – 2k - 2k) - 4 -k(2k - 2 + 2k)] = 0
1/2[-k + 1(-4) + k(6 - 4k) -4 - k(4k - 2)] = 0
1/2[4k - 4 + 6k - 4k2 - 16k + 8 - 4k2 + 2k)] = 0
1/2(-8k2 - 4k + 4) = 0
-8k2 - 4k + 4 = 0
-8k2 - 8k + 4k + 4 = 0
-8K(k + 1) + 4(k + 1) = 0
(k + 1) (4 - 8k) = 0
k + 1 = 0
k = -1
4 - 8k = 0
k = 4/8
k = 1/2
So, the value of k is -1 and 1/2 .
Question 9 |
If a connected graph G has planar embedding with 4 faces and 4 vertices, then what will be the number of edges in G?
7 | |
6 | |
4 | |
3 |
For any(connected) planar graph with v vertices, e edges and faces, we have
V - E + F = 2
= 4 - E + 4 =2
E = 4 - 2 + 4
E = 6
Question 10 |
What is the area bounded by the parabola 2y = x2 and the line x = y - 4?
18 | |
36 | |
72 | |
6 |
and the line x = y – 4 ------ (2)
Then y = x+4
Now, Substitute Y value in Equation-(1)
x2 = 2 ( x + 4 ) ------ (3)
Solving equation-3 we get x = 4, - 2.
Place Values of x in equation (1) and (2) we will get y = 8, 2.
Then the points of intersection are (8, 4), (2, –2).
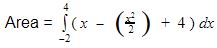
After solving the integration, we will get 18.
Question 11 |
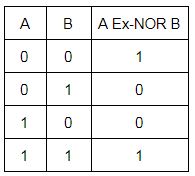
The following circuit represents the function of a 2–input __________ logic gate.
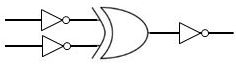
Exclusive-OR
| |
Exclusive-NOR
| |
NAND
| |
NOR
|
Step-2:
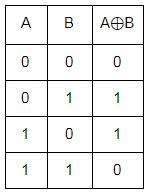
Step-3: We have to apply not operation then we are getting Ex-NOR.
Question 12 |
What is the possible number of reflexive relations on a set of 5 elements?
225
| |
215 | |
210
| |
220
|
Step-2: The possible number of reflexive relations on a set of 5 elements 2(n2-n) which is 220 for n=5.
Question 13 |
XML documents form a ___ structure.
Binary tree
| |
Tree
| |
Linear list | |
Graph |
→ This specification does not specify how the document entity is to be located by an XML processor; unlike other entities, the document entity has no name and might well appear on a processor input stream without any identification at all.
Question 14 |
Banker’s algorithm is used for:
Deadlock avoidance | |
Deadlock recovery
| |
Deadlock resolution
| |
Deadlock prevention
|
Question 15 |
Which one of the following is most affected by the presence of outliers in sample data?
Variance
| |
Mean
| |
Median
| |
Mode
|
For the sample data set:
1, 1, 2, 2, 2, 2, 3, 3, 3, 4, 4
We find the following mean, median, mode, and standard deviation:
Mean = 2.58
Median = 2.5
Mode = 2
Standard Deviation = 1.08
If we add an outlier to the data set:
1, 1, 2, 2, 2, 2, 3, 3, 3, 4, 4, 400
The new values of our statistics are:
Mean = 35.38
Median = 2.5
Mode = 2
Standard Deviation = 114.74
Note: Outliers often has a significant effect on your mean and standard deviation.
Question 16 |
Consider the matrix A defined as follows:

What is the eigenvalue of 3A3 + 5A2 - 6A + 21, where I is an identity matrix?
4, 110, 10
| |
1, 27, -8
| |
1, 9, 4
| |
4, 27, 9
|
Eigenvalues of A3 are 1, 27 and –8.
Eigenvalues of A2 are 1, 9 and 4.
Eigenvalues of A are 1, 3 and –2.
Eigenvalues of I are 1, 1 and 1.
∴ The eigenvalues of 3A3 + 5A2 – 6A + 2I.
First eigenvalue = 3(1) + 5(1) – 6(1) + 2(1) = 4
Second eigenvalue = 3(27) + 5(9) – 6(3) + 2(1) = 110
Third eigenvalue = 3(–8) + 5(4) – 6(–2) + 2(1) = 10
∴ The required eigenvalues are 4, 110, and 10.
Question 17 |
If A and B are sets and AUB = A∩B, then which of the following is correct?
A=B | |
A=∅
| |
B=∅ | |
A⊂B
|
= x belongs to A intersection B
= x belongs to A and x Belongs to B
= x belongs to B
so A subset of B --- (2)
Now we will let y belong to B which implies y belongs to A U B
= y belongs to A intersection B
= y belongs to A and y belongs to B
= y belongs to A
Therefore, B subset of A --- (3) from (2) and (3) we get A=B.
Question 18 |
What is the total number of spanning trees of a complete graph of 4 vertices (K4)?
16 | |
8 | |
4 | |
15 |
nn-2 = 42 = 16
Question 19 |
Considering 0-address instructions machine, what will be the top of the stack after executing the following sequence of instructions?
PUSH 15, PUSH 4, PUSH 6, MULT, PUSH 30, ADD, ADD
30 | |
69 | |
54 | |
10 |
Step-1: PUSH 15,PUSH 4 and PUSH 6 from bottom to top. Now top of the stack value is 6.
Step-2: Perform MULT operation. 6*4=24. Now present stack values are from bottom is 15 and 24.
Step-3: Next again PUSH 30. Now top of the stack is 30.
Step-4: Perform ADD operation. 30+24=54
Step-5: Now present stack values are from bottom is 15 and 54. Perform ADD operation.
Step-6: 15+54=69
Question 20 |
The maximum number of boolean functions that can be formed using 3 boolean variable is ____.
512 | |
256 | |
128 | |
1024 |
→ For three Boolean variables (n = 3), there are 23 = 8 different cases, giving us a total of 28
= 256 Boolean functions of 3 variables.
Question 21 |
Which of the following statements is/are correct?
-
(i) If the rank of the matrix of given vectors is equal to the number of vectors, then the vectors are linearly independent.
(ii) If the rank of the matrix of given vectors is less than the number of vectors, then the vectors are linearly dependent.
Both (i) and (ii)
| |
Only (ii)
| |
Only (i) | |
Neither (i) nor (ii) |
→ You can think of an r x c matrix as a set of r row vectors, each having c elements; or you can think of it as a set of c column vectors, each having r elements.
→ The rank of a matrix is defined as (a) the maximum number of linearly independent column vectors in the matrix or (b) the maximum number of linearly independent row vectors in the matrix. Both definitions are equivalent.
For an r x c matrix,
1. If r is less than c, then the maximum rank of the matrix is r.
2. If r is greater than c, then the maximum rank of the matrix is c.
→ The rank of a matrix would be zero only if the matrix had no elements. If a matrix had even one element, its minimum rank would be one.
